Recommended Quick Tour
-

It’s the Internet of PEOPLE
1:54 -

Knowing WHO is in your space
Shifting the paradigm from
1:41
good-guy/bad-guy to who are you? -
Didn't we already solve this?
We didn't, for a number of reasons – but we're ready now.
4:11 -

The transformative power of PKIDR™ digital signatures
8:14 -

Accountable Anonymity™ on the information highway
2:16 -

No Excuses now.
The misunderstandings and resistance that have prevented PKI from delivering on its promise.
5:33
The Big Picture
-
AUTHENTICITY™ Big Picture High-altitude view

A new coalition of time-tested ideas
3:57
to rescue our information infrastructure. -
The QUIET ENJOYMENT Revolution It's time for something completely different

Things are NOT working.
2:20
A big problem requires a big change. -
Elements of Authenticity™

How the essential parts of
4:26
Authenticity™ work together. -
We Can Fix This!

AUTHENTICITY™ is the solution
8:29
hiding in plain sight. -
You Know More About Security Than the Security Experts

Real security is rooted in
10:56
common sense you've learned in daily life. -
Definition of Authenticity™

A four-line definition that ties
00:40
together the essential elements. -
Boiling the Ocean Hatsopoulosophy and a thousand burners
How can such a big transformation
4:21
possibly be accomplished?
History
-
What Happened? Why security technology has failed us

It seemed like the right thing
4:42
at the time - but old assumptions wear out,
and now we're in dangerous territory. -
Sara's Question Wasn't PKI supposed to fix all that?
Didn't we already solve this?
4:11
We didn't, for a number of
reasons - but we're ready now. -
Two Sad Stories
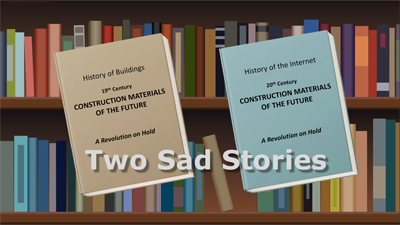
It's not the first time a solution-in-waiting
9:41
has taken decades to be realized. -
The Seeds of Authenticity™ Fixing the Internet
Wes Kussmaul describes the genesis of his vision for Authenticity™ – "accountability with privacy."
7:51
PKI 
-
What is AUTHENTICITY™? Accountable, REAL people

We've never held PKI
3:57
to its full promise. NOW is the time. -
PKI in Action The heartbeat of Authenticity™

Does it sound too good
5:27
to be true? It's not. Here's how it works. -
What Does PKI Stand For? Something old, something new

That name is part
1:26
of the misunderstanding. -
Ten Reasons Why PKI has been waiting until now to fix our security problems

The misunderstandings and resistance
5:41
that have prevented PKI from delivering
on its promise. -
PCN and PEN Calculation The math behind the magic
How your computer creates
1:15
your Puzzle Kit -
What Does DONE RIGHT Mean? Building out PKI’s full potential

Seven elements that expand
8:10
traditional PKI into the full power
of Authenticity™
Digital Signatures
These heroes of Authenticity seem almost like magic.
Here's how they work.
-
OMG! The Transformative Power of PKIDR™ Digital Signatures

PKIDR™ digital signatures are what
8:14
makes Authenticity™ work -
Digital Signatures The Real Thing

NOT the same as
2:31
"electronic signatures"! -
The Fix
Examples of digitally signed
4:01
items with the remarkable power of ACCOUNTABILITY. -
Digital Signatures Unchained

Digital signatures are not
6:28
just for blockchain.
Fake News
-
The Reporter's Credential Digital signatures take aim
Digitally signed stories
2:02
are a powerful weapon against fake news. -
Fake Videos ACCOUNTABILITY to the rescue

Phony videos, altered videos,
1:30
and deep fakes will not survive in
a world of digital signatures.
Identity Quality
Multifactor Authentication
Privacy
-
PrivacyOwn your information

From your PKI-secured digital file
4:47
cabinet, release your information under
license and NDA. -
The BillboardDoing business by the roadside
Don't be surprised when
2:29
big trucks come by and load up your stuff. -
BurglarsInvaders in your information home
Stealing information, planting tracking devices,
5:11
and creating secret doors for themselves. -
Farms

The big business of breeding and selling personal information. It's time to ESCAPE!
5:42

Tired of being owned?
Silicon Valley, the NSA, and the botnet builders intend to own you. Read this book to find out how to prevent it.
Get the book
Governance (Osmio)
Worldwide DULY CONSTITUTED PUBLIC AUTHORITY
-
AUTHENTICITY™ Big PicturePeople, governance, technology

A new coalition of time-tested ideas
1:58
to rescue our information infrastructure. -
The City of Osmio
An ancient and respected concept
2:23
retooled for the global digital age. -
The Right Way to Certify

You should own and govern the vital records
14:24
department that attests to your identity. -
Does Centralized Authority Make You Nervous?
Just as you own the city where
2:32
you live, you - the online
resident - own the City of Osmio. -
What Happened on March 7The founding of the City of Osmio

Crafting its Municipal Charter
10:20
at the ITU in Geneva 2005. -
World City HallWes Kussmaul speaks at the UN

Authenticity, PKI, Osmio,
10:46
and duly constituted public authority.
Blockchain
-
Accountable Blockchain

Adding ACCOUNTABLE ANONYMITY™
2:22
to blockchains to thwart bad actors. -
Digital Signatures Unchained

Digital signatures are
6:28
not just for blockchain.
IoT
Synthentic Identities
National Security
Enterprise Authenticity
Authenticity and your business
Whether your network is cloud-based or on premises, chances are you have outsiders such as contractors, suppliers, distributors, and others accessing your precious digital assets. Learn how a program of enrollment to digital identity certificates and a policy of DSE — digital signatures everywhere — will bring pervasive accountability, and with it real security, to your enterprise.
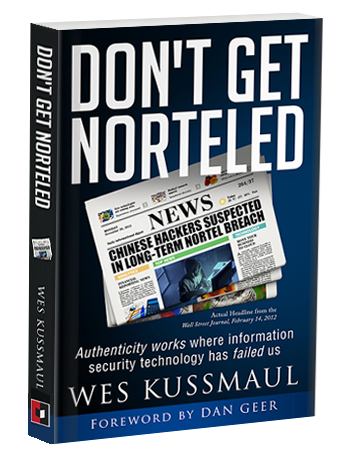
This breach caused 1000 times the $250 million losses of the Equifax incident
Security technology is not working. Without measurably reliable identities and accountability, your door is wide open to nefarious action by intruders and inside bad actors. Read how the unthinkable happened to a multi-billion-dollar company that spiraled into astonishingly quick bankruptcy because of a shockingly elementary — and preventable — breach.
Why has it taken so long?
No excuses now!
-
Ten ReasonsWhy PKI has been waiting until now to fix our security problems

The misunderstandings and resistance
5:41
that have prevented PKI from delivering
on its promise. -
Two Sad Stories And one happy ending
It's not the first time a solution-in-waiting
9:41
has taken decades to be realized. -
Sara's Question Wasn't PKI supposed to fix all that?
Didn't we already solve this?
4:11
We didn't, for a number
of reasons - but we're ready now.